Cyberattacks are getting smarter every day, which has increased the concerns of security. This is where threat detection and response (TDR) comes in. It can be considered as your digital security guard that can spot dangers (like hackers or viruses), act fast to stop attacks and protect your data before damage happens.
In this blog, we will understand TDR in simple terms. What it is, why it matters, and how it keeps businesses safe.
What is Threat Detection and Response?
Threat Detection and Response (TDR) is a collection of procedures and tools used to recognize, evaluate, and address cybersecurity threats. It makes sure that businesses protect themselves from possible threats as soon as possible. Imagine TDR as a 24/7 security force for your online existence. It does two enormous things:
- Identifies sneaky threats (viruses, hackers, scams).
- Acts quickly to boot them out.
If you don’t have it, hackers might stroll on in, swipe your passwords, or take down your systems, and you won’t even realize it until it is too late.
How does threat detection work? (The Digital Alarm System)
Your computer can’t scream ‘HELP! A HACKER IS HERE!’ So, TDR tools do the screaming for it. Here is how:
- Behavior Watch: If a file begins behaving strangely (such as sending data to a mysterious server at 3 am), an alarm sounds.
- Pattern Checks: Threat Detection and Response knows the difference between regular traffic (you are logging in to Gmail) vs. suspicious activity (1000 failed logins in 5 seconds).
- AI & Machine Learning: some tools use smart tech to predict attacks before they happen by learning from past threats.
- Real-life example: If your bank sees someone trying to withdraw money from India while you are asleep in Texas, that is threat detection in action. It will block such fraud before money disappears.
What Happens When a Threat is Found? (The “Response” Part)
Finding hackers is step one. Stopping them is where the magic happens. A good TDR system:
- Contains the Threat: Such as confining a zombie in an isolated room so that it can’t infect anyone else.
- Stop Attacks: Blocks hacker tactics. It deletes malware, blocks malicious IPS, or disables infected accounts (such as phony emails with malware links).
- Warns You: Provides a “Hey, we just protected you!” alert.
- Facts: Some systems can even strike back by booting hackers out of your network automatically!
Why Do You Need Threat Detection and Response?
Because hackers don’t make any difference between a CEO and a social media user, here's why TDR is important to everyone:
For Companies:
- A single attack can cost millions in damages, legal fees, and lost trust (and reputations are ruined).
- Compliance laws (like GDPR, HIPAA, and PCI DSS) require strong security measures.
For Individuals:
- Hackers steal identities, empty bank accounts, or hijack social media accounts.
- Weak security on your device can help hackers spread malware to others.
For the Internet:
- Each vulnerable device is a potential doorway for bigger attacks (such as ransomware propagating through networks).
How Do You Increase Your Threat Detection and Response?
Want to remain safe? Here is your action plan:
For Individual:
- Good Antivirus: Free ones are better than nothing, but paid software (such as Bitdefender) catches more threats.
- Update Everything: Phones, app routers, hackers target old, unpatched software.
- Remain Skeptical: if an email is “Urgent! Click Now!” It is likely a scam.
For Businesses:
- Invest in Advanced Tools: Spend on EDR (Endpoint Detection & Response) and XDR (Extended Detection & Response) which offer greater protection (sophisticated TDR tools that detect sophisticated attacks).
- Train Employees: Human error accounts for 90% + of breaches. Train employees to recognize phishing emails.
- Automate Threat Hunting: AI-powered tools scan networks 24/7 for unknown threats.
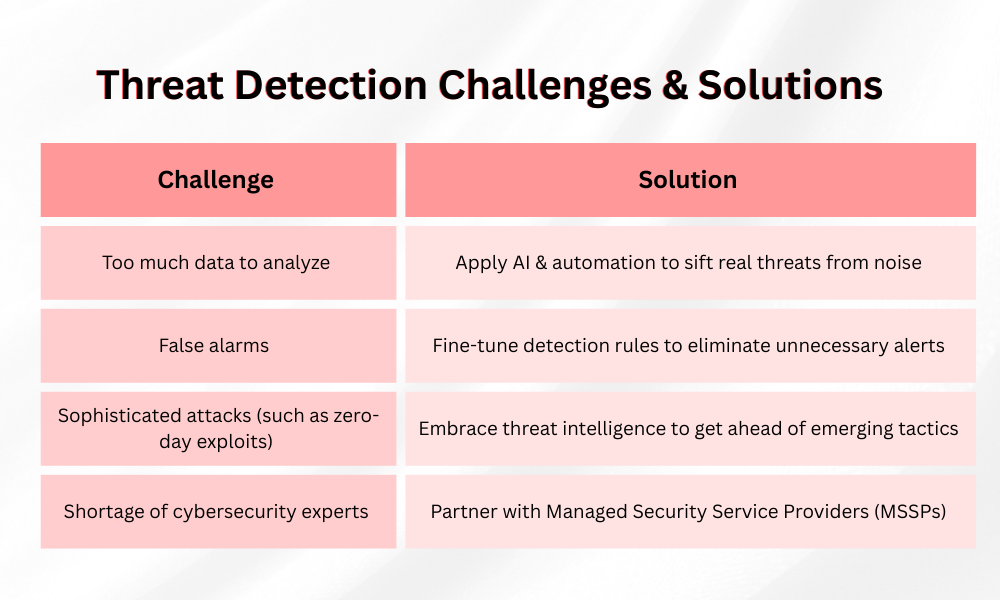
Challenges in Threat Detection and Response & How to Overcome Them
Even the greatest systems encounter obstacles:
The Future of Threat Detection and Response
Hackers are getting trickier day by day. Cyber guardians are fighting back to such attacks! TDR will soon:
- Use More AI & Predictive Security: Machines will forecast attacks before they occur.
- Global Threat Sharing: Security teams around the globe share threat information in real-time.
- Simpler Protection: One-click security measures for easy, hassle-free safety.
Be Proactive, Don’t Be Suspicious
Use threat detection and response tools like a digital seatbelt. Stay aware, take simple steps, and let the TDR system do the work.
Your Next Steps:
- Individuals: Get your devices updated, turn on multi-factor authentication (MFA), and be vigilant.
- Businesses: Test your security, employee training, and examine more sophisticated TDR options.
Cyber threats will evolve continuously, but with proper defenses, you can remain ahead of the game.
Need more cybersecurity tips? Check out SecureITWorld today!
FAQ
Q1. Is threat detection and response only for big companies?
Answer: Nope! Even your home Wi-Fi needs basic protection (like a firewall and antivirus).
Q2. Can TDR stop all hackers?
Answer: Nothing’s 100% hack-proof, but TDR slashes your risks by 90%+.
Q3. What’s the #1 threat TDR stops?
Answer: Ransomware, where hackers lock your files and demand money to unlock them.
Also Read: Dark Web Monitoring and Its Contribution to Mitigate Cyberthreats