Retrieval-augmented generation (RAG) makes a major leap in how computer systems collect and utilize information. It allows computers to pull in relevant data from various sources, rather than depending on what they learned during their initial training.
When a question is asked, the system searches through a collection of documents, finds the most relevant information, and then uses that context to create a precise and informed response. This approach comes with its own set of security challenges, which will be discussed in the blog below.
By combining generative models with outside data sources, RAG generates new, possibly vulnerable paths. Hackers may attempt to exploit the connection between the generation and retrieval processes, add erroneous data, or change the information that has been obtained.
What is Retrieval-Augmented Generation (RAG)?
A retrieval mechanism and a generative model are two essential elements that are combined in Retrieval-augmented generation (RAG), a computational technique that improves information processing. RAG finds the most pertinent information about a given query by first searching through a sizable knowledge base.
Advanced methods like vector embeddings and semantic search are used in this retrieval process to convert text into numerical representations that are easily compared and matched. Retrieval-augmented Generation is especially effective for applications that need precise, accurate, and up-to-date information synthesis because it produces a more accurate, contextually rich response that can draw upon specific and current information.
How It Works?
Consider yourself engaged in a particularly challenging jigsaw puzzle. However, you can use a large library that contains all possible components, not just the ones you now have. This is how Retrieval-augmented generation (RAG) works. A search process that goes through a vast number of documents or knowledge bases is initiated by the entry of a query.
Information that is retrieved is integrated by the model in a smooth manner. It is kind of like a writer who is looking up the relevant books to cite, right before writing a paper. The system does not just repeat the information already known to it, but the process combines the context with the background knowledge in intelligent ways.
RAG system uses the latest NLP models to parse the query, convert the text to mathematical representations, and perform similarity searches among document embeddings. The algorithms are designed to select the most relevant information, so that only the most pertinent context is given.
Security Risks With RAG-
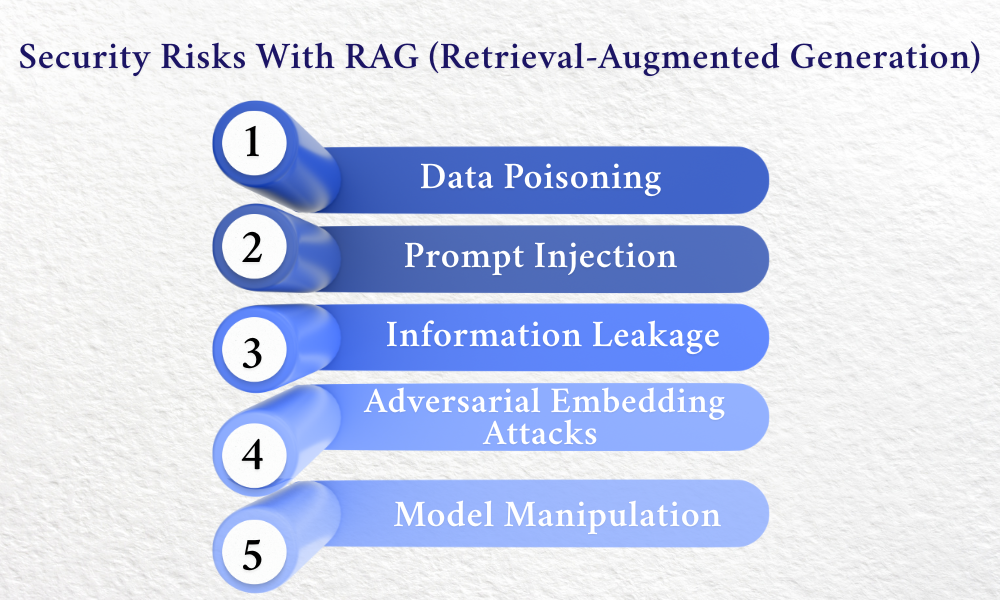
1. Data Poisoning
Malicious attackers can intentionally insert false or tampered data into the knowledge base employed by Retrieval-augmented generation. Attacking the source documents or vector database can mislead the retrieval process, where the system ends up producing incorrect or misleading outputs.
2. Prompt Injection
Carefully designed input prompts may take advantage of weaknesses in the RAG system, misleading it into divulging confidential information or evading targeted security measures. Adversaries create tailored prompts that manipulate retrieval and generation operations to pull in unwanted information or bypass inherent safety mechanisms.
3. Information Leakage
Sensitive or private information from the knowledge base may unintentionally be leaked during the RAG retrieval process. In the absence of robust access restrictions and filters, the system might retrieve and include privileged material in generated answers, which could lead to security and privacy breaches.
4. Adversarial Embedding Attacks
Sophisticated attackers may be able to design specially crafted vector embeddings that are semantically similar to authentic data. Such tampered embeddings have the potential to mislead the RAG system's similarity search algorithms and cause it to retrieve and utilize maliciously designed information during the generation process.
5. Model Manipulation
Attackers could be able to influence the Retrieval-augmented generation system's behavior by deliberately focusing on the knowledge base and underlying retrieval procedures. This may lead to reactions that are skewed, controlled, or compromised and do not perform as intended.
How To Protect RAG Systems?
A multi-layered security model is necessary to protect RAG systems; companies should have strong input filtering systems that clean up queries and prevent possible injection attacks; and methods such as embedding space sanitization, which keeps an eye on and cleans up vector representations, can prevent adversaries from tampering with retrieval mechanisms.
The second most essential line of defense is the deployment of continuous monitoring and dynamic security protocols. That involves having active tracking mechanisms set up to evaluate retrieval behavior patterns, spot malicious behavior, and raise instant warnings on likely security incidents. Incorporating state-of-the-art encryption of vector databases, regularly cycling access credentials, and defining permission granularity structures minimizes vulnerability extensively.
How To Mitigate RAG Security Risks?
Put in Place Granular Access Controls
Restricting who can access and modify your RAG system's knowledge base is necessary to maintain security. Establish a comprehensive permission framework that grants different levels of access to systems and users. One approach to do this is to create role-based access controls that limit retrieval and modification capabilities based on user credentials.
Ongoing Observation and Threat Detection
Systems for real-time monitoring should be put in place so that possible security concerns can be quickly detected and addressed. Provide sophisticated tracking systems that monitor system activity continuously, identify odd retrieval patterns, and highlight possible security flaws.
Employ Robust Data Validation Techniques
Implementing rigorous data validation is the primary protection against security concerns for Retrieval-augmented generation (RAG) systems. Strict input screening protocols must be implemented in order to thoroughly review data prior to its entry into the system.
Regular Maintenance of the Knowledge Base
It's an ongoing process to maintain the knowledge base in your RAG system. Implement regular cleaning and verification procedures to eliminate information that is outdated, redundant, or potentially compromised. Develop systematic review procedures that enable you to regularly check the sources and content of the information repositories.
RAG systems will increasingly become the backbone of trustworthy AI interactions. While we use this system for precision, we must remain vigilant in securing them from the various challenges mentioned above.
For more informational content, keep visiting us at SecureITWorld.
Read More: The Linguistic Divide: AI’s Language Barriers Threaten Global Inclusion